WGU D488 OA Study Guide II - 2025 | Mastering Cybersecurity 📖
Welcome to your cybersecurity crash course! You stand as a network protector who fights against cybercriminals who attempt to cause chaos. Scanning networks and stopping cyber villains fulfills many of the secret lair fantasies even though it is far from being a real superhero experience.
WGU D488 students need to learn about three fundamental concepts for their course which are:
- Advanced Persistent Threats (APTs): APTs are prolonged, targeted cyberattacks that aim to steal information over time. They typically involve stealthy, highly skilled attackers infiltrating networks.
- Incident Response Phases (Preparation, Detection, Containment, Recovery): The phases include preparing systems for potential attacks, detecting security breaches, containing the threat to prevent further damage, and recovering systems to normal operation.
- Network Scanning and Enumeration Tools (e.g., Nmap, Nessus): Nmap is used for network mapping and vulnerability scanning, while Nessus helps identify security flaws by scanning networks and systems for known vulnerabilities.
By the end of this, you’ll be ready to tackle WGU D488 OA questions and secure your digital domain with confidence. So, let’s dive into these essential cybersecurity concepts and get you closer to becoming a network security pro!
How to Use This Guide for the WGU D488 OA Exam?📖
The D488 Cybersecurity Architecture and Engineering OA exam at WGU evaluates your understanding of cybersecurity threats, incident response processes, and network security tools. This guide simplifies the key concepts of Advanced Persistent Threats (APTs), the incident response phases (Preparation, Detection, Containment, Recovery), and network scanning and enumeration tools (e.g., Nmap, Nessus) to help you grasp the topics tested in the exam.
We also provide exam-style questions and practical applications to ensure you’re fully prepared for the questions on the WGU D488 OA exam.

Understanding Advanced Persistent Threats (APTs) For D488 OA📝
Advanced Persistent Threats (APTs) represent the most severe security threats that exist in the cybersecurity domain. What constitutes an APT attack and why would it matter to you require explanation.
What is an APT?
Threats from Advanced Persistent Threats involve hackers permanently infiltrating your network system so they stay undetected for terms ranging from months to years. Stealing sensitive information remains the main objective for perpetrators instead of pursuing fast system breakdown or destructive action. This could be anything from government secrets to intellectual property or financial data. APT attacks are often carefully planned and executed using sophisticated techniques to avoid detection. Unlike simple attacks that might just crash a system or steal passwords, APTs aim to maintain a persistent presence in the network.
Who’s Behind APTs?
APTs are often carried out by well-funded, highly skilled attackers. These attackers are usually from one of three groups:
- Nation-states: Some governments use APTs to spy on other nations or to gather military intelligence.
- Cybercriminals: Smaller, but highly skilled hacker groups may perform APTs for financial gain or to steal valuable business secrets.
- Hacktivists: These are groups with a political or social agenda that use APTs to promote their cause, like disrupting systems they disagree with.
What Drives APT Attacks?
The reasons behind APTs can vary, but here are the most common motivations:
- Cyber Espionage: Stealing confidential information such as state secrets or corporate intellectual property.
- Financial Gain: Cybercriminals may steal financial data or funds to make a profit.
- Hacktivism: Political or social activists may attack to disrupt systems or steal information that supports their cause.
- Destruction: Sometimes, the goal is to simply cause damage or disrupt operations, though this is less common in APTs.
How APTs Work: The Attack Process
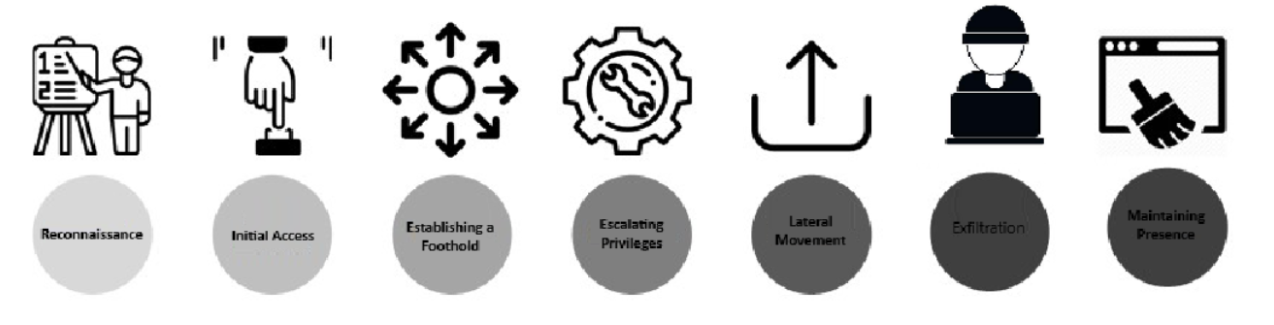
Understanding how APTs unfold is crucial in defending against them. These attacks usually follow several stages:
- Reconnaissance: First, the attackers gather information about the target—this could involve looking at public data, scanning networks, or using social media to gather intelligence.
- Initial Access: Attackers use various methods like phishing emails or exploiting software weaknesses to gain access to the target’s network.
- Establishing a Foothold: Once inside, attackers install malware or backdoors to maintain access. This way, they can come back later if their initial entry is discovered.
- Escalating Privileges: Attackers will try to gain more control by elevating their access, often by using stolen credentials or password cracking to gain administrator rights.
- Lateral Movement: They move through the network, infecting more systems and gathering more information.
- Exfiltration: The attackers will then steal sensitive data, like financial records, intellectual property, or confidential documents, and move it to their own servers.
- Maintaining Presence: Even after their objectives are achieved, APT actors try to stay inside the network, sometimes for months, to continue gathering information or prepare for future attacks.
Evasion Tactics Used by APTs
To stay undetected, APT actors use a variety of clever techniques:
- Encryption: They may encrypt their communication to avoid detection.
- Anti-Forensic Measures: Hackers often try to erase their tracks or cover up their presence to make it harder for defenders to trace them.
- Legitimate Credentials: Some APT attackers use stolen user credentials to blend in with normal, everyday activity on the network, making their presence harder to notice.
Who Do APTs Target?
While APTs can target any organization, they usually go after those with high-value information, such as:
- Government agencies
- Large corporations
- Defense contractors
- Financial institutions
- Critical infrastructure like energy grids or healthcare systems
Even smaller companies that are part of the supply chain of these larger organizations can become targets, as they might provide a backdoor to a bigger prize.
How to Detect and Defend Against APTs
Defending against APTs requires a strong, multi-layered security approach. Some strategies include:
- Holistic security: Using a combination of different security tools that work together seamlessly.
- Continuous monitoring: Regularly checking networks for unusual activities.
- Threat intelligence: Staying updated on the latest trends in cyber threats.
- Incident response: Having a plan in place for how to respond if an APT is detected.
- Employee training: Educating workers about phishing and other social engineering tactics that attackers use to get into systems.
APTs and WGU D488
Students should grasp the challenging nature and defensive strategies for APTs while studying WGU D488 Cybersecurity Architecture and Engineering. Your knowledge of APT characteristics and their methods alongside defense strategies will enable you to engineer secure systems while assessing vulnerabilities during real-life threat responses.
By mastering these concepts, you’ll be better equipped to handle WGU D488 OA questions that require you to analyze and respond to the challenges posed by APTs.
Understanding Incident Response Phases For D488 OA📝
The incident response procedure in cybersecurity involves both the management and the response phase of security attacks or security breaches. The main objective consists of fast issue detection followed by containment actions and recovery steps before enhancing overall system protection to reduce future occurrences. The four essential stages of incident response consist of Preparation followed by Detection after which Containment measures occur before Recovery steps.
Phase 1: Preparation
A good incident response plan requires effective preparation as its base. You need to set up the necessary security systems alongside qualified staff to manage any security emergencies that may arise. This section outlines what you should do during preparation:
- Creating an Incident Response Plan (IRP): Your team needs a tested Incident Response Plan (IRP) to explain everything they should do during incidents. It shows each team member what actions to follow.
- Training and Awareness: It’s not enough to have a plan—you need to make sure everyone knows what to do. That means regular training for your incident response team and educating other employees about security best practices.
- Tools and Resources: You need the right tools, such as security monitoring systems and software, to detect and respond to incidents. This is the time to make sure everything is ready to go when a threat emerges.
Phase 2: Detection
Detecting security issues as soon as possible allows you to control and fix them more swiftly. The detection phase starts with finding out whether an attack has happened. Here’s how it works:
- Monitoring: Regularly checking your system and network activity enables you to find abnormal behavior quickly. Look for irregular user logins combined with unexpected traffic rises that unauthorized persons try to access.
- Incident Alerts: Setting up alert systems helps detect when something unusual is happening. For example, if a system tries to access a file it normally wouldn’t, an alert will notify the response team.
- Log Analysis: Logs are records of events on your systems, and analyzing them helps uncover any hidden threats or anomalies.
Phase 3: Containment
You need to start containing the attack after discovery. Quantifying attacks allows you to halt their movement and prevent further damage to the system. Here are the steps to take:
- Short-Term Containment: You would set apart the infected systems from your network’s other devices. Disconnecting the affected device from the network stops attackers from spreading to other parts.
- Long-Term Containment: After short-term containment, it’s important to implement long-term measures to ensure that the attacker can’t return. This might involve applying security patches or updating access controls.
Phase 4: Recovery
The security recovery process starts when the attack is contained followed by a restoration of regular business functions. The recovery process requires fixing all damage while making systems ready for future use:
- Restoring Systems: When restoring systems one must either retrieve backups to recover the systems or remove software to reset the systems to their original state.
- Monitoring: Even after recovery, continue monitoring the systems to make sure the attacker doesn’t find a way to get back in.
- Lessons Learned: An incident analysis should be conducted to learn from what transpired after any event has been resolved. This review process achieves two goals: It enables you to develop better preparation strategies and it improves your response actions for upcoming events.
Best Practices in Incident Response
- Clear Communication: Keep all stakeholders informed throughout the process. Communication helps ensure everyone is on the same page and knows what to do next.
- Team Coordination: The incident response team should work together seamlessly. Clear roles and responsibilities ensure that actions are taken quickly and effectively.
- Documentation: Keep detailed records of everything. This helps during recovery, and the data can also be used for legal or forensic investigations later on.
Incident Response and WGU D488
The Cybersecurity Architecture and Engineering course (WGU D488) requires full comprehension of incident response phases to manage as well as stop cybersecurity threats. The educational curriculum will instruct students to develop their skills in security incident response from detection through preparation and containment and recovery stages to become effective in authentic security situations. This knowledge will also be helpful for answering WGU D488 OA questions on incident management and response strategies.
Tired of reading blog articles?
Let’s Watch Our Free WGU D488 Practice Questions Video Below!

Understanding Network Scanning and Enumeration Tools For D488 OA 📖
Network scanning and enumeration establish the fundamental processes that reveal network structure in addition to its security status and exposed weaknesses for security professionals. Security professionals use these methods to actively measure network security status while discovering safety risks to maintain network integrity.
What is Network Scanning?
Network scanning identifies all the devices that function on and interact with a particular network. The network scan process reveals all devices present within the network including servers as well as routers switches and firewalls. This process typically begins with using IP addresses to locate active devices.
What is Network Enumeration?
After scanning, network enumeration follows. This step involves gathering more detailed information about the devices on the network. You’ll probe systems to uncover things like:
- Operating systems
- Applications
- User accounts
- Running services
The data collected through enumeration is crucial for understanding the security landscape of the network.
Key Features of Network Scanning and Enumeration
- Device Discovery: The network discovery process discovers all linked server hardware alongside router switches as well as firewalls and other network devices.
- Port Scanning: System port scanning involves examining active open ports to determine the operational services connected to those ports.
- Vulnerability Scanning: Through vulnerability scanning systems and networks along with devices get examined for security weaknesses that attackers can leverage.
Active vs. Passive Scanning
There are two main types of scanning methods:
- Active Enumeration: This method involves directly probing a target system to gather information. While this method can provide more detailed results, it can also alert the system being scanned.
- Passive Enumeration: The process of passive enumeration achieves information acquisition through methods that do not involve active interaction with the target system. Publicly available information serves as the foundation for this method to make its discovery less likely by the target.
Common Tools for Network Scanning and Enumeration
Several tools are used in network scanning and enumeration. Here are some of the most common ones:
- Nmap: Network exploration and security auditing rely on Nmap since it stands as an open-source tool that delivers versatility and high power to its users. Through special packet responses, Nmap executes its functions which include port scanning and both version discovery and operating system identification.

- Nessus: A commercial tool used for vulnerability scanning. Nessus can perform various scans to detect security flaws in systems, applications, and networks, including port scanning and OS detection.

- OpenVAS: An open-source alternative to Nessus, OpenVAS offers comprehensive vulnerability scanning and is used to identify weaknesses in systems and applications.

The Importance of Network Scanning and Enumeration
Network scanning along with enumeration serves as a fundamental security mechanism for cybersecurity operations during penetration testing. The processes reveal issues to vulnerabilities before their discovery by attackers which enables organizations to repair weaknesses and strengthen their security systems. Timely network scans play an essential role in preventing your system from new security threats.
Ethical Considerations in Network Scanning
Security professionals need network scanning tools to perform their duties however these tools can fall into the wrong hands of malicious actors who misuse them. The Stuxnet virus orchestrated its facility penetration through network enumeration techniques against Iran’s nuclear facilities. Ethical guidelines must accompany network tool use because these methods must remain compliant with legal standards.
Network Scanning and Enumeration in WGU D488
Understanding network scanning and enumeration techniques is a fundamental requirement for WGU D488 Cybersecurity Architecture and Engineering students who need to conduct successful cybersecurity assessments. Students who learn how to operate Nmap and Nessus properly become ready to detect system weaknesses and construct defense systems while handling security threats. Additionally, students will need this knowledge to answer WGU D488 OA questions related to network security and scanning.
Wrapping Up Your Cybersecurity Journey: A Must-Know Guide for WGU D488 OA Success📖
You have now completed an important deep analysis of all aspects of APTs Incident Response Phases Network Scanning and Enumeration Tools. These fundamental cybersecurity concepts should be firmly established in your knowledge which will permit you to protect your network from threats and maintain its safety.
Your progress through WGU D488 requires retaining these practical cybersecurity concepts because they will help defend against actual cyberattacks. These cybersecurity concepts function as vital instruments that anyone working in cybersecurity manages in their day-to-day activities while defending networks.
Closely review the essential topics because WGU D488 OA includes tests on these specific knowledge points. Successful execution of the WGU D488 OA requires your expertise in analyzing while detecting and responding to cybersecurity threats. Put aside enough time to review the material while practicing because practice represents your best path to success.
Your studies will benefit from good luck while you understand that cybersecurity means mastering digital defense techniques instead of just protecting networks. You’ve got this!