WGU D488 OA Study Guide I - 2025 | Risk Assessment, Zero Trust, and BYOD Security📖
Cybersecurity isn’t just for IT professionals in dark rooms staring at code—it’s something that affects everyone in today’s digital world. Whether you’re shopping online, logging into work remotely, or even just scrolling social media, cybersecurity threats lurk everywhere. Organizations are in a never-ending battle to protect sensitive data, and they use strategic security frameworks to do just that. This is where risk assessment, Zero Trust Architecture (ZTA), and BYOD security frameworks come into play.
- Quantitative vs. Qualitative Risk Assessment: Quantitative risk assessment measures risks in numerical terms, like potential financial loss, while qualitative risk assessment evaluates risks based on likelihood and impact without using numbers.
- Zero Trust Architecture (ZTA): ZTA is a security model where no user or device is trusted by default, even if they are inside the network. It requires continuous verification before granting access to resources.
- BYOD Security Frameworks: These frameworks are designed to manage and secure personal devices (Bring Your Own Device) within an organization, ensuring compliance with security policies and protecting sensitive data.
This article presents clear explanations about the three topics to benefit WGU D488 OA students along with security professionals who need to grasp these essential concepts. Cybersecurity awaits your immersion in a level never experienced before.
How to Use This Guide for the WGU D488 OA Exam?📖
The D488 Cybersecurity Architecture and Engineering OA exam at WGU evaluates your understanding of risk assessment methodologies, security architectures, and device security frameworks. This guide simplifies the key concepts of quantitative vs. qualitative risk assessment, Zero Trust Architecture (ZTA), and BYOD security frameworks to help you grasp the topics tested in the exam.
We also provide exam-style questions and practical applications to ensure you’re fully prepared for the questions on the WGU D488 OA exam.

Quantitative vs. Qualitative Risk Assessment: Understanding the Difference For D488 OA📝
Risk assessment stands as an essential element for security operations in cybersecurity. Companies will always confront various risks that include cyberattacks along with data breaches and financial losses coming from insecure systems. Organizations use two core risk assessment procedures namely quantitative and qualitative risk assessment to effectively handle their security risks.
We should start by defining these general concepts before moving ahead. A quantitative risk assessment functions like computer math by working with numerical values and probably distributions and specific numbers. The method of qualitative risk assessment functions as an expert-driven approach that utilizes descriptions and categories to make risk evaluations.
Practitioners who work in cybersecurity need to understand these assessment approaches because they must design risk management strategies that meet specific frameworks which include NIST or ISO. This knowledge is also valuable for those preparing for WGU D488 OA questions.
What is Quantitative Risk Assessment?
The method of Quantitative Risk Assessment (QRA) works to numericize various risks. Security incidents can be evaluated through this method which measures their financial potential based on specific data points. Cognitive risk assessment aims to develop systematic procedures for objective risk analysis.
Key Components of Quantitative Risk Assessment
- Single Loss Expectancy (SLE): This is the financial loss expected from a single occurrence of a threat. It’s calculated using:
- Example: If a server worth $10,000 is expected to lose 50% of its value in a cyberattack, the SLE is $5,000.
- Example: If a server worth $10,000 is expected to lose 50% of its value in a cyberattack, the SLE is $5,000.
- Annualized Rate of Occurrence (ARO): This estimates how often a risk is expected to happen in a year.
- Example: If a malware attack is expected to occur twice a year, the ARO is 2.
- Example: If a malware attack is expected to occur twice a year, the ARO is 2.
- Annualized Loss Expectancy (ALE): This measures the yearly financial impact of a risk and is calculated using:
- Example: If the SLE is $5,000 and ARO is 2, the ALE is $10,000 per year.
- Example: If the SLE is $5,000 and ARO is 2, the ALE is $10,000 per year.
- Cost-Benefit Analysis: After calculating ALE, organizations compare it to the cost of implementing security controls. If a security measure costs less than the ALE, it is considered a good investment.
Advantages of Quantitative Risk Assessment
- Objective and data-driven – Uses financial figures to justify cybersecurity investments.
- Repeatable and consistent – Since it’s based on numbers, different people analyzing the same data will likely reach similar conclusions.
- Helps prioritize risks – The most expensive risks can be addressed first.
However, QRA has limitations. It depends heavily on accurate data, which isn’t always available. If the probabilities or costs are miscalculated, the assessment can be misleading.
What is Qualitative Risk Assessment?
Unlike QRA, qualitative risk assessment (QLRA) does not rely on exact numbers. Instead, it focuses on descriptions, categories, and expert opinions to evaluate risks.
Key Components of Qualitative Risk Assessment
- Risk Likelihood: This represents how likely a risk is to occur, often categorized as Low, Medium, or High instead of using probabilities.
- Example: If a company frequently experiences phishing attempts, the likelihood of a successful attack might be labeled as “High.”
- Example: If a company frequently experiences phishing attempts, the likelihood of a successful attack might be labeled as “High.”
- Risk Impact: This describes the severity of the consequences if a risk materializes, often categorized as Low, Medium, or High as well.
- Example: A minor software bug may have a “Low” impact, whereas a ransomware attack could have a “High” impact.
- Example: A minor software bug may have a “Low” impact, whereas a ransomware attack could have a “High” impact.
- Risk Matrix: A risk matrix is a visual tool used to map out the likelihood and impact of risks. It helps prioritize which risks need immediate attention.
- Example: A risk that is “High” in likelihood and “High” in impact would be given the highest priority.
- Example: A risk that is “High” in likelihood and “High” in impact would be given the highest priority.
- Subject Matter Expertise: Since qualitative assessments rely on expert judgment, cybersecurity professionals, IT staff, and executives discuss and evaluate risks together.
Advantages of Qualitative Risk Assessment
- Simple and fast – Does not require complex calculations.
- Useful when numerical data is unavailable – Some risks, like reputation damage, are hard to quantify.
- Encourages collaboration – Brings different departments together to discuss security concerns.
However, qualitative assessments can be subjective—different people may rate the same risk differently. It also doesn’t provide precise financial data, making it harder to justify security investments.
Comparing Quantitative and Qualitative Risk Assessment
Feature | Quantitative Risk Assessment | Qualitative Risk Assessment |
Basis | Uses numbers and financial data | Uses categories and expert judgment |
Measurement | Measured in exact figures | Measured in Low, Medium, and High ratings |
Example Calculation | ALE = SLE × ARO | Risk Matrix with Likelihood vs. Impact |
Accuracy | More precise, but depends on reliable data | More flexible, but subjective |
Best For | Large organizations with financial data | Smaller businesses or when data is unavailable |
In real-world cybersecurity strategies, many organizations use a hybrid approach—combining both methods. The company deploys numerical assessment for financial planning purposes yet uses descriptive methods to identify risks that lack numerical representation.
Organizations need Zero Trust Architecture (ZTA) to challenge traditional trust models while performing continuous verification checks throughout all access points because risk assessment alone does not provide full protection.
Zero Trust Architecture (ZTA) For D488 OA📝
Since the advent of digital technology the complexity level of cyber threats has continuously risen. Traditional security paradigms maintain that all components found in an organizational network deserve trust regardless of their identity. Modern business operations that rely on cloud platforms combined with remote work policies and employee usage of personal technology make the previous trust assumption obsolete. Zero Trust Architecture (ZTA) serves as the solution for these needs.
The fundamental principle of Zero Trust security is to prevent trust by conducting ongoing verification. Organizations using ZTA require users and devices to perform identity verification with continuous authentication procedures and minimum permission access despite their physical location.
Understanding ZTA is crucial for cybersecurity professionals and students preparing for WGU D488 OA questions. It is a modern approach that strengthens security by eliminating implicit trust and continuously verifying all access attempts.

Core Principles of Zero Trust
ZTA is built on three fundamental principles:
- Terminate Every Connection – Unlike traditional security models that trust certain devices or users, Zero Trust verifies and inspects every connection before allowing access. Even encrypted traffic is analyzed in real-time to detect threats.
- Protect Data Using Granular Policies – Access requests are validated based on factors such as user identity, device type, location, and data sensitivity. Policies are continuously reassessed to ensure security.
- Reduce Attack Surface by Eliminating Implicit Trust – Users connect directly to applications and resources rather than broad network access, reducing the risk of lateral movement by attackers.
The guidelines protect organizations from security risks by providing secure remote work possibilities for their employees.
Five Pillars of Zero Trust Architecture
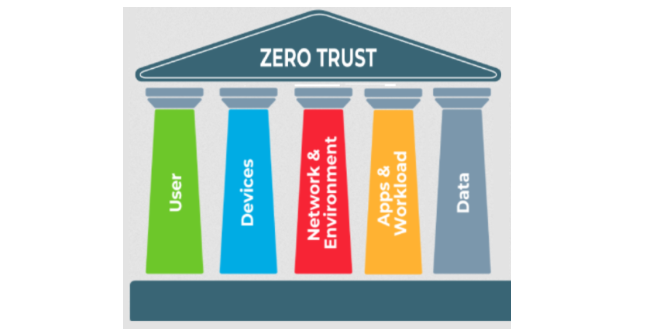
The Cybersecurity and Infrastructure Security Agency (CISA) outlines five key pillars for implementing ZTA:
- Identity Management – The strict enforcement of authentication together with authorization methods allows users to access only permitted system areas. For strong security organizations must implement both Multi-factor authentication (MFA) and least privilege access components.
- Device Security – Every device attempting to access an organization’s resources is continuously verified for security compliance.
- Network Security – Traditional network perimeters are replaced with micro-segmentation, meaning networks are broken into smaller, secure zones to limit movement by attackers.
- Application and Workload Protection – Security controls are applied directly to applications and workloads rather than relying on network location.
- Data Security – Organizations must identify, classify, and monitor sensitive data, ensuring that only authorized users can access it.
Implementing Zero Trust: Key Strategies
Transitioning to a zero-trust model requires changes in identity management, network security, and access policies. Below are essential strategies for implementing ZTA:
1. Identity and Access Controls
- Enforce strong identity governance by implementing MFA, passwordless authentication, and identity verification for every login attempt.
- Use policy-based access controls, granting permissions based on role, device, location, and other contextual factors.
2. Network Segmentation and Isolation
- Implement micro-segmentation, which divides networks into small, isolated sections to prevent attackers from moving freely.
- Deploy software-defined perimeters (SDP) that create secure overlay networks, making critical resources invisible to unauthorized users.
3. Continuous Verification and Monitoring
- Use real-time monitoring tools like Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) systems.
- Implement behavior-based detection to identify and block anomalous activities before they cause harm.
4. Least Privilege and Adaptive Access Controls
- Apply just-in-time access strategies, granting access for limited time periods when needed.
- Use Attribute-Based Access Control (ABAC), which considers various attributes (user identity, location, device type) before granting access.
Benefits of Zero Trust Architecture
Adopting ZTA offers numerous advantages, making it one of the most effective cybersecurity models today:
1. Enhanced Security Against Cyber Threats
- Prevents data breaches by verifying every access attempt.
- Reduces the attack surface by limiting unnecessary access.
- Mitigates insider threats by continuously monitoring user behavior.
2. Improved Operational Efficiency
- Simplifies security policy creation and enforcement across cloud and on-premise environments.
- Enables secure remote work by granting access based on identity rather than physical location.
- Provides better visibility into security events and incidents.
3. Cost Savings and Compliance
- Reduces long-term security costs by preventing expensive data breaches.
- Simplifies compliance with regulations like HIPAA, GDPR, and NIST by enforcing strict access controls.
- Enhances auditing and reporting capabilities.
Zero Trust vs. Traditional Security Models
Feature | Traditional Security | Zero Trust Architecture |
Trust Model | Trusts users inside the network | Never trusts; always verifies |
Access Control | Broad access once inside | Least privilege access only |
Perimeter Security | Focuses on network firewalls | Uses micro-segmentation and identity verification |
Threat Response | Limited monitoring inside the network | Continuous monitoring and real-time response |
Adaptability | Struggles with cloud, BYOD, and remote work | Designed for modern, flexible environments |
Users obtain comprehensive access inside the network after they pass through security protocols based on traditional models. Every network request is treated as untrusted before verification with Zero Trust security approaches which lowers cyber threats.
The adoption of Zero Trust Architecture requires enterprises to implement BYOD Security Frameworks since they verify personal devices align with strict security rules while keeping device usage flexible.
Tired of reading blog articles?
Let’s Watch Our Free WGU D488 Practice Questions Video Below!

BYOD Security Frameworks For D488 OA📖
The majority of workplace employees now choose to use their own smartphones as well as laptops and tablets for their work assignments which take place in the digital environment. The implementation of Bring Your Own Device (BYOD) allows workers to bring personal equipment but creates substantial security problems. Organizations need to build extensive BYOD security systems that safeguard critical data without disrupting employee productivity scales.
A well-defined BYOD security strategy ensures that organizations balance accessibility with robust security measures. Understanding these frameworks is essential for cybersecurity professionals and students preparing for WGU D488 OA questions.
The Importance of BYOD Security Frameworks
The combination of remote work trends and cloud-based applications forces organizations to establish BYOD policies as mandatory system elements. The advantages of more flexibility affect employees favorably yet organizations encounter difficulties in protecting valuable corporate data that resides on staff members’ personal gadgets. Companies without dedicated BYOD security standards face considerable threats to their data security which include unauthorized access alongside data breaches and malware infections as well as compliance violations.
Model corporate data protection frameworks combine administrative policies with technologies and operational practices to maintain workplace confidentiality while permitting worker utilization of private devices. Such frameworks deliver instructions regarding device oversight together with user permission structures and security mandates with emergency response capabilities to reduce organizational threats.
Key Components of a BYOD Security Framework
Device Management
Organizations need to take proper control of personal devices that handle corporate data to achieve effective BYOD security. Mobile Device Management (MDM) solutions enable organizations to implement security policies that they monitor for compliance across connected devices. MDM tools provide companies with capabilities to control their security settings in addition to enabling encryption measures and permitting them to wipe corporate data from breached devices remotely.
To ensure security, organizations should require employees to register their devices before granting access to corporate resources. Compliance monitoring ensures devices have up-to-date security patches and strong passwords, and meet encryption standards.
Identity and Access Management (IAM)
Controlling access to company resources from personal devices is essential for security. Organizations must implement Multi-Factor Authentication (MFA) to ensure that only authorized users access sensitive data. Additionally, Role-Based Access Control (RBAC) ensures employees only access the information necessary for their job functions, reducing exposure to sensitive data.
By integrating Single Sign-On (SSO), employees can securely log in to multiple applications using one set of credentials, improving both security and user experience.
Security Policy Enforcement
Employees must comply with security policies that clarify their ability to work using personal devices. A properly organized Acceptable Use Policy (AUP) specifies employee rules for handling data together with authorization standards and software use requirements.
Organizations should enforce:
- Data Protection Standards – Encrypt corporate data and back up important files regularly.
- Network Security Requirements – Ensure employees connect to secured networks (e.g., VPNs) when accessing corporate resources remotely.
- Application Whitelisting – Restrict access to unapproved applications that may introduce security vulnerabilities.
Incident Response and Risk Mitigation
Security incidents can still happen despite establishing preventive measures. Every organization must create precise response plans for occurrences such as device loss or theft data breaches and malware attacks.
Employees need clear procedures to report security issues that they encounter at work. Regular security audits performed by IT teams help to find weaknesses and strengthen BYOD security programs.
Best Practices for Securing BYOD Environments
To create a secure BYOD environment, organizations should follow industry best practices:
- Regular Policy Updates and Compliance Checks
- Update security policies to keep pace with evolving threats.
- Conduct periodic security training to educate employees on cyber risks.
- Enforce automatic security updates on all BYOD devices.
- Network Segmentation and Access Control
- Use Virtual Private Networks (VPNs) to encrypt communications.
- Segment networks to limit unauthorized access to sensitive data.
- Device and Application Security
- Require antivirus software installation on BYOD devices.
- Implement whitelisting and blacklisting to manage application access.
Comparing BYOD Security with Traditional IT Security
Feature | Traditional IT Security | BYOD Security Framework |
Device Ownership | Company-owned | Employee-owned |
Access Control | Managed by IT | Hybrid approach with IAM policies |
Security Measures | Centralized policies | Requires MDM and employee compliance |
Flexibility | Limited to corporate devices | Supports personal devices securely |
Unlike traditional security models that control all devices centrally, BYOD security frameworks require a flexible yet stringent approach to protect corporate data while maintaining employee productivity.

Your WGU D488 OA Cybersecurity Journey: Mastering Risk Assessment, Zero Trust, and BYOD Security📖
Examining Quantitative vs. Qualitative Risk Assessment, implementing Zero Trust Architecture (ZTA), and designing BYOD Security Frameworks will help you succeed in cybersecurity beyond standard tests. These foundational cybersecurity principles serve as cornerstones to develop robust security measures that protect businesses both when using strict verification policies managing BYOD environments and conducting threat assessments.
As you move forward in your WGU D488 OA journey, take the time to grasp these principles thoroughly. These topics will appear on your final OA, so mastering them now will not only help you succeed academically but also in your future cybersecurity career.
Stay curious, stay secure, and keep learning! Best of luck on your WGU D488 OA, and may your cybersecurity knowledge always stay one step ahead of the threats!